Top of Page
- Links to move inside this page.
- HOME
- Investor Relations
- Management Policy
- Business Philosophy and Mid-term Plan
Business Philosophy and Mid-term Plan
Business philosophy
IIJ Group's business philosophy (raison d'etre or purpose) is as follows.
As the company name "Internet Initiative Japan Inc." suggests, we are committed to the ongoing pursuit of initiatives in the field of Internet technology, which is one of those technological innovations that might occur once in a century, and contributing to the development of the networked society by providing groundbreaking services and platforms that propose new uses for the network.
To develop network infrastructure through technological innovation
We are committed to the ongoing pursuit of initiatives in the field of Internet technology to open up the future of the digital society through new value created by ever faster networks and computing.
To provide solutions (IT services) that supports a networked society
We continuously develop and introduce highly reliable and value-added IT services that anticipate changes taking place around the world, to support the use of networks by society and individuals.
To provide meaningful opportunities for growth to our employees (a place where human resources with diversified talents and values can play an active role)
We aim to offer meaningful working opportunities for growth through business, in which our staff can take a proactive approach to technical innovation and social contribution, and actively demonstrate their abilities with pride and a sense of satisfaction. We aspire to be a company where employees are never satisfied with the status quo, and are always thinking about the future world, contributing to social development, and achieving personal growth through work that has value for society.
IIJ Group Mid-term Plan (FY2024-FY2026) and Mid-to-Long Term Vision
Financial targets
| Consolidated Financial Targets | FY2026 | |
|---|---|---|
| Business Expansion | Total revenue | Around JPY380 billion (FY2026 outlook: JPY385.0 billion) |
| Profitability | Operating Profit | Around JPY46 billion (FY2026 outlook: JPY38.5 billion) |
- (*)Please refer to 4Q25 earnings release
 announced on May 14, 2026 for FY2026 financial outlook.
announced on May 14, 2026 for FY2026 financial outlook.
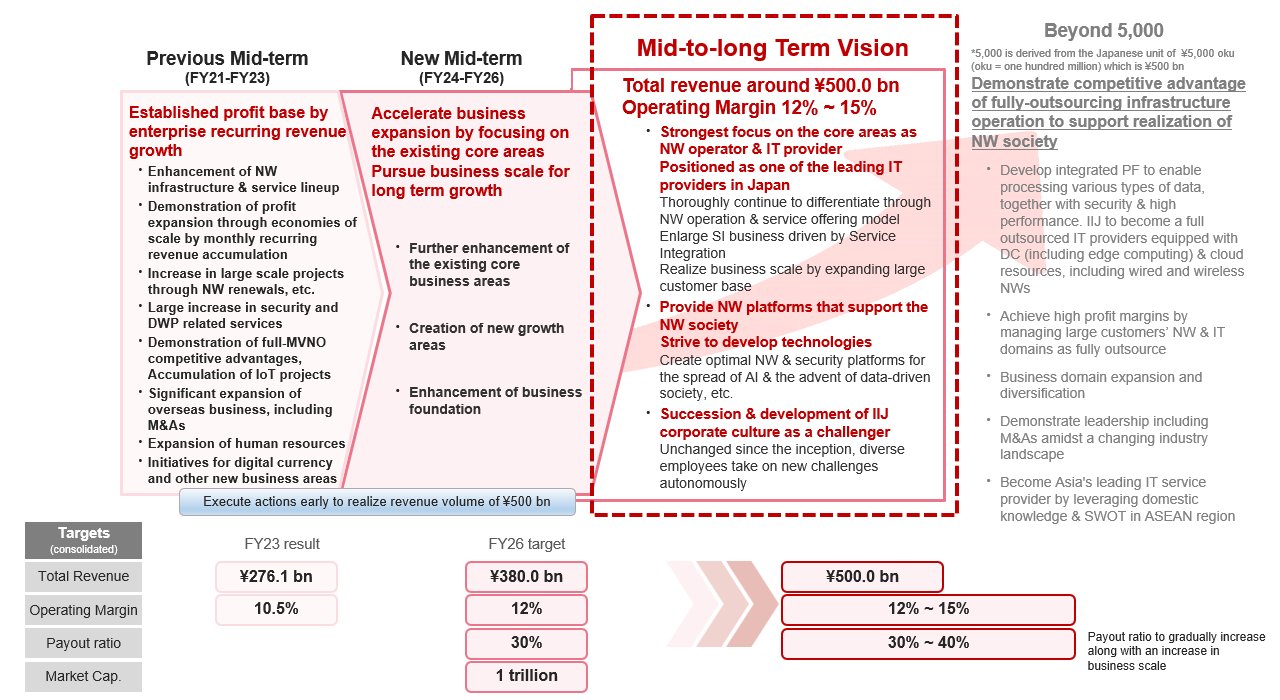
Mid-to-Long Term Vision and the positioning of the New Mid-term Plan
In order to effectively fulfill our business philosophy, we recognize that it is highly important to continuously expand our business scale while leveraging the strengths of our group. Triggered by the COVID-19, IT utilization among Japanese private and public sectors has finally accelerated, and the market is expected to continuously expand further over the mid-to-long term. Under such recognition, we have formulated the Mid-to-Long Term Vision that includes growth to total revenue volume of JPY 500.0 billion (consolidated) as a milestone we should aim for in the mid-to-long term, as described on the next page. The New Mid-term Plan is positioned as an important growth path and process to reach toward the Mid-to-Long Term Vision over the next three years.
IIJ Group Mid-term Plan (FY2024-FY2026)
Under the New Mid-term Plan, the fundamental vision of our business remains unchanged. We are proud that we had created Internet in Japan as a communication infrastructure and environment by bringing in diverse talents who autonomously demonstrate their abilities. Based on our advanced Internet-related technology, we will develop high value-added network services, stably operate Internet-related networks and systems, and provide systems integration functions to meet the IT demands of Japanese companies. Through implementing these actions, we play our role fully and pursue our business expansion. In particular, considering our business situation such as the increase in large-scale network construction projects with multi-year contracts through Service Integration in FY2023, we will accelerate revenue growth and thereby enhance profit levels by rigorously strengthening our existing core business areas. We will also focus our efforts on new areas for the next phase of growth. We also continue to enhance our business foundation to realize these. Details and targets are as follows.
Further enhancement of the existing core business area:
- (ⅰ)We will increase the scale of large transactions and the number of customers by advancing composite transactions further through the acquisition and execution of large-scale network construction and operation projects from customers in various industries in the form of Service Integration. We will drive revenue growth through systems integration.
- (ⅱ)We will enhance profitability by realizing economies of scale through the continuous accumulation of enterprise recurring revenue such as network services, including those derived from Service Integration. We will drive profit growth through network services.
- (ⅲ)In response to increasingly sophisticated and complex security demands, we will further enhance our line-up of high value-added services. We continue to differentiate ourselves through stable and high-quality network operations toward the era of DX realization. We will create platform services that support the utilization of AI and Data Lake.
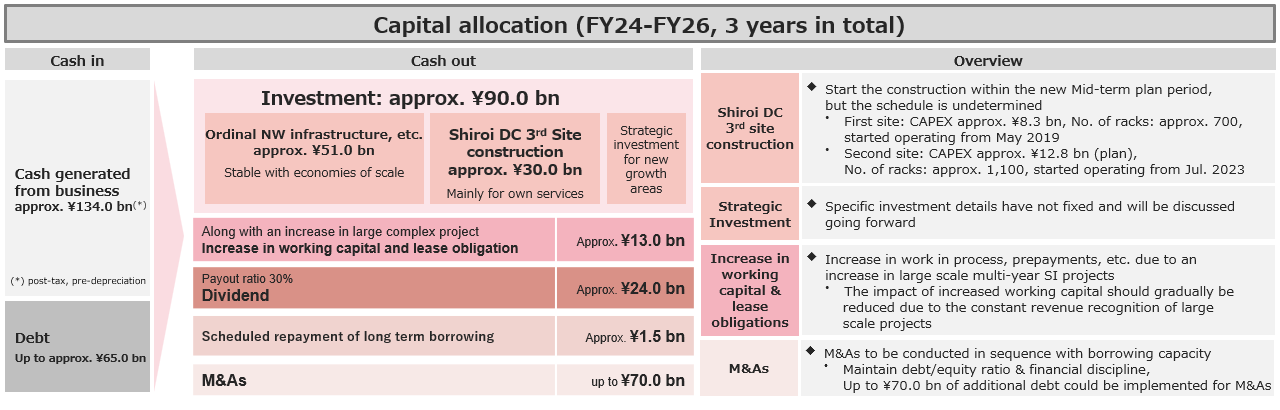
- (ⅳ)We continue to optimally expand network infrastructure to support business expansion. We plan to make construction investments in the third site of the Shiroi Data Center to accommodate our service equipment in the future.
Creation for new growth area:
- (ⅰ)Commercialization towards realizing a data-driven society: We will consider and begin to create a business model that expands the service area of data analysis and distribution, which was initiated during the previous Mid-term Plan, actively generates meaningful data to society, and establishes and operates an information circulation system that enables to function smoothly for multiple purposes.
- (ⅱ) Spread of digital currency (DCJPY) in Japan: We aim for the state of digital currency business currently being developed by DeCurret DCP Inc., to begin spreading in Japan as practical projects, with further market growth expected.
Enhancement of operation and business foundation:
- (ⅰ)We continue to strengthen and expand human resource recruitment and focus on developing next-generation management resources who lead our organization and businesses.
- (ⅱ)We will respond properly to external factors such as rising labor costs and other costs including passing cost rises onto selling prices.
- (ⅲ)We continue to pursue M&A opportunities, primarily to acquire additional human resources necessary for business growth.
- (ⅳ)We continue to address management with an emphasis on sustainability and strengthening governance in line with our business growth, which we have already been promoting since before. We plan to introduce an executive remuneration system that is linked to the achievement of the New Mid-term Plan, and further share the enhancement of corporate value with shareholders.
- (ⅴ)As projects become larger, we aim to improve the sophistication of business and project management methods, especially in systems integration. We carry out appropriate capital allocation and balance sheet management in response to investments in large-scale data center and an increase in working capital.
Capital Allocation
- (*)As for the result of "IIJ Group Mid-term Plan (FY2021-FY2023)," please refer to "IIJ Group Mid-term Plan (FY2024-FY2026)" and Mid-to-Long Term Vision 1. Result of the previous Mid-term Plan
 .
.
End of the page.