Top of Page
- Links to move inside this page.
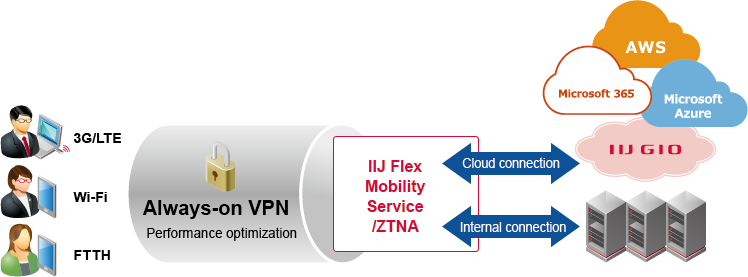
IIJ Flex Mobility Service/ZTNA
About the Service Overview
IIJ Flex Mobility Service/ZTNA is a remote access service that implements Zero Trust.
The service eliminates sluggish operation and constant disconnections, problems with conventional remote access, and provides features that implement Zero Trust, such as communication visualization, detailed policy settings, and access control.
The service also greatly supports applications that require real-time connection, such as Web meetings, conference calls, and virtual desktops.
Service Features
Web meetings without disconnections and latency
Web meetings, such as Microsoft Teams, will be free of video or audio disruptions. Meetings can run smoothly as if everyone were in the same office.
Implementation of Zero Trust
Various connections can be controlled, such as by forcing VPN connection, to mitigate security risks caused by telework. This takes care of troublesome security measures.
Hassle-free communication
Provide hassle-free remote access anytime, anywhere. Our unique VPN technology ensures stable connections and low latency.
Secure connection control
Implement Zero Trust to protect corporate data. Access control is enabled by determining the connection time, location, and end device in real time.
Grasp of detailed usage and risks
Visualize all traffic leaving devices. This helps grasp the communication status of telework and diagnose communication troubles.
(Japanese text only)
- Related Contents
End of the page.
